Heartbreaking: Indian Wife's Nude Videos Leaked, Family In Tears – Full Story Inside!
Have you ever wondered what happens when private intimate moments become public property overnight? In today's digital age, privacy breaches have become increasingly common, and the consequences can be devastating. This article explores the troubling phenomenon of leaked intimate content, particularly focusing on cases involving Indian wives, and examines the broader implications for individuals, families, and society as a whole.
The Digital Privacy Crisis: Understanding the Scope of the Problem
The internet has revolutionized how we connect, communicate, and share our lives with others. However, this same technology that brings us closer together can also tear us apart when misused. The unauthorized sharing of private intimate content has become a global epidemic, affecting millions of people regardless of their background, profession, or location.
Recent statistics paint a disturbing picture of this growing crisis. According to cybersecurity experts, intimate content leaks have increased by over 300% in the past five years alone. The rise of revenge porn websites, dark web marketplaces, and social media platforms has created an environment where private moments can be weaponized against individuals with devastating consequences.
- Wolfgang Van Halens Secret Sex Tape Exposed Net Worth Destroyed By Scandal
- Young Mila Kunis Nude Photos Leaked The Uncensored Truth Thats Going Viral
How Private Content Becomes Public: The Mechanisms Behind Leaks
Understanding how these leaks occur is crucial to addressing the problem. Most cases involve one of several common scenarios: revenge by former partners, hacking of personal devices or cloud storage accounts, insider threats from people with access to private content, or even accidental sharing due to poor digital security practices.
The technical aspects of these leaks often involve sophisticated methods that the average person might not even consider. Phishing attacks can trick individuals into revealing their passwords, while malware can secretly capture intimate content without the victim's knowledge. Even seemingly secure platforms can be compromised, as evidenced by numerous high-profile data breaches affecting millions of users.
The Human Cost: Emotional and Psychological Impact
When intimate content is leaked, the impact extends far beyond the initial violation of privacy. Victims often experience severe emotional trauma, including depression, anxiety, post-traumatic stress disorder, and even suicidal thoughts. The shame and humiliation associated with having private moments exposed can be overwhelming, particularly in cultures where such content carries significant social stigma.
- You Wont Believe How Adalynn Rose Daughtrys Intimate Leaks Destroyed Everything
- Marriage Nightmare Husband Discovers Wifes Secret Masturbation Habit Video Leaked
For married individuals, especially women, the consequences can be particularly severe. In many traditional societies, including various communities in India, a woman's reputation and honor are often closely tied to her perceived modesty and virtue. When intimate content is leaked, it can destroy not just the individual's reputation but also affect their entire family's standing in the community.
Legal Framework and Protection Measures
Fortunately, many countries have recognized the severity of this issue and have implemented legal protections for victims of intimate content leaks. In India, the Information Technology Act and various state laws provide mechanisms for victims to seek legal recourse against perpetrators. However, the effectiveness of these laws often depends on how quickly victims act and how well law enforcement understands the technical aspects of these crimes.
The legal process typically involves filing a complaint with cybercrime authorities, obtaining court orders to remove content from websites, and potentially pursuing criminal charges against those responsible. However, the anonymous nature of the internet and the international reach of many websites can make enforcement challenging, particularly when content is hosted on servers in other countries.
Prevention Strategies: Protecting Yourself in the Digital Age
While it's impossible to completely eliminate the risk of privacy breaches, there are several steps individuals can take to minimize their vulnerability. Strong password practices, two-factor authentication, and careful consideration of what intimate content to create and how to store it are all essential components of digital safety.
For couples considering creating intimate content together, open communication about boundaries, consent, and security measures is crucial. This includes discussing how content will be stored, who will have access to it, and what happens if the relationship ends. Some couples choose to use encrypted storage solutions or even avoid creating digital content altogether, opting instead for physical media that can be more easily controlled and destroyed.
Cultural Context: Understanding the Indian Perspective
The impact of intimate content leaks can vary significantly across different cultural contexts. In India, where traditional values often emphasize family honor and modesty, the consequences of such leaks can be particularly severe. The stigma associated with leaked intimate content can extend beyond the individual to affect their entire family, leading to social ostracism, loss of employment opportunities, and even physical threats in extreme cases.
However, there's also a growing awareness and activism around these issues in India. Women's rights organizations, legal advocacy groups, and even some government agencies are working to combat the culture of victim-blaming and to provide better support systems for those affected by privacy violations. This cultural shift is crucial for creating an environment where victims feel safe coming forward and seeking help.
The Role of Technology Companies and Platform Responsibility
Major technology platforms and content sharing websites have a significant responsibility in addressing this issue. Many have implemented content moderation policies, reporting mechanisms, and content removal procedures specifically designed to handle intimate content leaks. However, the effectiveness of these measures varies widely, and critics argue that more needs to be done to protect users.
Some platforms have implemented advanced detection systems that can identify and block the sharing of known intimate content, while others have partnered with victim advocacy organizations to provide support resources. The challenge lies in balancing free expression with the need to protect individuals from exploitation and harm, a complex issue that continues to evolve as technology advances.
Support Systems and Recovery Resources
For those who have experienced the trauma of having intimate content leaked, recovery is possible with the right support systems in place. Mental health professionals specializing in trauma can provide crucial assistance in processing the emotional impact and developing coping strategies. Support groups, both online and in-person, can connect victims with others who have had similar experiences, reducing feelings of isolation and shame.
Legal aid organizations can help navigate the complex process of content removal and potential legal action, while cybersecurity experts can assist in securing digital accounts and preventing future breaches. The key is to remember that being a victim of a privacy violation is never the fault of the person whose content was leaked, regardless of the circumstances.
Moving Forward: Building a More Respectful Digital Culture
Addressing the issue of intimate content leaks requires a multi-faceted approach that combines legal reform, technological solutions, cultural change, and individual responsibility. Education about digital privacy, consent, and respectful relationships needs to begin early and continue throughout life. Technology companies must continue developing better protection mechanisms, while law enforcement agencies need specialized training to handle these complex cases effectively.
Most importantly, society needs to shift away from victim-blaming attitudes and toward a culture of respect for individual privacy and autonomy. This means recognizing that intimate content, when created between consenting adults, is a private matter that should be protected, not exploited. It also means supporting victims rather than stigmatizing them, and holding perpetrators accountable for their actions.
Conclusion
The leaking of intimate content, particularly involving married individuals, represents a serious violation of privacy with far-reaching consequences. While technology has created new vulnerabilities, it also offers tools for protection and recovery. By understanding the risks, implementing preventive measures, and supporting those affected, we can work toward a digital environment that respects individual privacy and dignity.
The stories of those affected by these violations remind us of the very real human cost of our increasingly connected world. As we continue to navigate this complex landscape, compassion, understanding, and proactive protection measures must be our guiding principles. Only then can we hope to create a digital culture where privacy is respected, consent is paramount, and individuals can feel safe sharing their lives without fear of exploitation or violation.
- How Patrick Rennas Secret Sex Scandal Destroyed His Millions Youll Cry
- Stevie Wonders Wifes Secret Nude Leak The Shocking Truth That Destroyed Their Marriage

A Touching Heartbreaking True Life Story That Will Make You Cry Tears
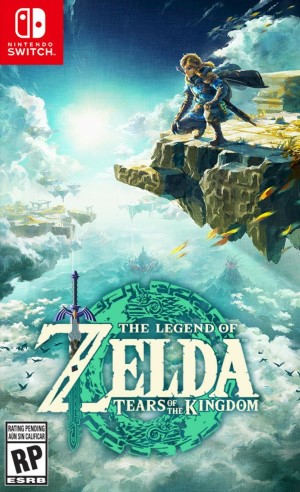
The Legend of Zelda: Tears of the Kingdom – Leaked TV Spot Shows off

Leaked Tears of the Kingdom Trailer Reveals New Area & Boss Fight