This "Leaked" Mother's Day Gift List Is Breaking The Internet And Your Wife's Heart (in A Good Way)!
Have you ever wondered what would happen if a secret Mother's Day gift list got leaked to the public? Well, that's exactly what's happening right now, and it's causing quite a stir online! This isn't just any ordinary gift guide - it's a treasure trove of thoughtful, creative, and downright ingenious gift ideas that are making wives everywhere swoon with delight. But before we dive into this heartwarming story, let's address a more serious concern that affects millions of people worldwide: data breaches and personal information security.
Understanding Data Breaches: Are You at Risk?
In today's digital age, data breaches have become alarmingly common. Every year, billions of personal records are exposed through various security incidents, leaving individuals vulnerable to identity theft, financial fraud, and other cybercrimes. The question is: could your personal information be among those compromised?
How to Check if Your Information Was Compromised
Find out if your personal information was compromised in data breaches by using specialized online tools designed to help you identify potential risks. These services scan through vast databases of leaked information to determine whether your email address, passwords, or other sensitive data have been exposed.
- Exposed Brooke Monks Age Fraud And The Leaked Porn That Broke The Internet
- You Wont Believe The Sex Secrets Glenn Becks Wife Just Exposed
Search your email on databreach.com to see where your data was leaked and learn how to protect yourself. This simple process can provide you with crucial information about potential vulnerabilities in your digital security. By entering your email address into these verification tools, you can quickly discover if you've been affected by any known data breaches.
The Impact of Data Leaks and How to Respond
How you can deal with data leaks now is crucial information for everyone in our interconnected world. Even if your information has been leaked, you can still minimize the impact and prevent online criminals from using your personal information for profit. The key is to act quickly and implement robust security measures.
When you discover that your data has been compromised, the first step is to change your passwords immediately. Use strong, unique passwords for each of your accounts, and consider enabling two-factor authentication wherever possible. Additionally, monitor your financial accounts closely for any suspicious activity and consider placing fraud alerts on your credit reports.
- You Wont Believe How Adalynn Rose Daughtrys Intimate Leaks Destroyed Everything
- Exclusive Leak Breckie Hills Private Shower Moment Goes Viral You Need To See This
Checking Your Personal Data Status
Check if your personal data has been compromised in known data breaches by using reputable online services. These platforms maintain comprehensive databases of known security incidents and can quickly cross-reference your information against their records.
Search over 18 billion breach records to get a comprehensive view of your digital footprint. This massive database includes information from countless websites, services, and platforms that have experienced security breaches over the years. The sheer volume of data underscores the importance of regular security checks.
Comprehensive Breach Directory Services
Breach directory check if your email or username was compromised search over 18 billion publicly leaked records need api access? Many services offer both free and premium options for checking your information against their extensive databases. Some even provide API access for developers and businesses who need to integrate these security checks into their own systems.
These comprehensive services allow you to search for your username and/or email address within publicly accessible lists of compromised accounts. The process is typically straightforward: simply enter your information, and the service will scan through millions of records to identify any matches.
Understanding the Scope of Data Breaches
Over 1.3 billion accounts across more than 100 websites and online services have been affected by data breaches in recent years. This staggering number highlights the widespread nature of the problem and emphasizes the importance of proactive security measures.
Major corporations, social media platforms, online retailers, and even government agencies have all fallen victim to data breaches. From credit card information to social security numbers, the types of data exposed vary widely, but the potential for harm remains constant.
A Lighthearted Break: The Leaked Mother's Day Gift List
Now, let's return to the heartwarming story that's capturing everyone's attention online. Mike Pence's leaked list of mother's day gift ideas for Karen Pence, aka Mother is published by Stephanie McMaster in The Haven, and it's taking the internet by storm. This delightful compilation of gift suggestions has struck a chord with people everywhere, offering both humor and genuine inspiration for celebrating the special women in our lives.
The list includes everything from classic gifts like flowers and chocolates to more creative and personalized options that show real thought and consideration. What makes this leak so special is its authenticity and the way it captures the essence of what makes Mother's Day meaningful - the thought, effort, and love behind each gift choice.
Protecting Yourself in the Digital Age
While we enjoy the lighthearted content making waves online, it's important to remember that data security remains a serious concern. Here are some practical steps you can take to protect yourself:
Regular Security Audits: Make it a habit to check your accounts for any signs of unauthorized access or suspicious activity. Set calendar reminders to perform these checks quarterly.
Strong Password Practices: Use a password manager to generate and store complex, unique passwords for each of your accounts. This prevents the domino effect that occurs when one account is compromised.
Two-Factor Authentication: Enable two-factor authentication wherever possible. This adds an extra layer of security by requiring a second form of verification beyond just your password.
Monitor Your Credit: Keep an eye on your credit reports and consider using credit monitoring services that alert you to any changes or suspicious activity.
The Psychology Behind Data Breaches
Understanding why data breaches occur can help you better protect yourself. Most breaches happen due to one of several common factors:
Human Error: Many breaches result from simple mistakes, like falling for phishing scams or using weak passwords. Education and awareness are key to preventing these types of incidents.
System Vulnerabilities: Outdated software and unpatched systems create opportunities for hackers to exploit weaknesses. Regular updates and security patches are essential.
Insider Threats: Sometimes, breaches occur due to malicious insiders or employees who have been compromised. Companies need robust internal security protocols to prevent these incidents.
What Companies Should Do to Protect Your Data
While individuals can take steps to protect themselves, companies also bear significant responsibility for safeguarding customer data. Here's what reputable businesses should be doing:
Regular Security Audits: Companies should conduct frequent security assessments to identify and address potential vulnerabilities before they can be exploited.
Data Encryption: All sensitive data should be encrypted both in transit and at rest, making it much harder for unauthorized parties to access even if they breach the system.
Employee Training: Staff should receive regular training on security best practices and how to recognize potential threats like phishing attempts.
Incident Response Plans: Companies need clear protocols for responding to data breaches, including notification procedures and remediation steps.
The Future of Data Security
As technology continues to evolve, so too do the methods used by cybercriminals. However, advancements in security technology are also progressing rapidly. Here are some trends to watch:
Artificial Intelligence: AI is being used both by attackers and defenders, with security systems increasingly relying on machine learning to detect anomalies and potential threats.
Blockchain Technology: Decentralized systems and blockchain are offering new ways to secure data and verify identities without creating centralized points of failure.
Biometric Authentication: Fingerprint scanning, facial recognition, and other biometric methods are becoming more common as alternatives to traditional passwords.
Conclusion
In a world where data breaches affect billions of accounts and personal information is constantly at risk, staying informed and proactive about your digital security is more important than ever. By regularly checking whether your information has been compromised, implementing strong security practices, and staying aware of the latest threats, you can significantly reduce your risk of becoming a victim of cybercrime.
At the same time, it's refreshing to see the internet light up with positive, heartwarming content like the leaked Mother's Day gift list that's bringing people together and spreading joy. Whether you're checking your data security or browsing gift ideas for the special women in your life, remember that staying informed and connected is what makes our digital world both challenging and wonderful.
Take the time today to check your accounts, update your passwords, and maybe even browse that viral gift list for some inspiration. Your digital security and your relationships are both worth investing in!
- Richard Geres Wife Sex Tape Scandal The Leaked Evidence That Broke The Internet
- Kanyes Wife Bianca In Shocking Sex Tape Leak Full Video Inside
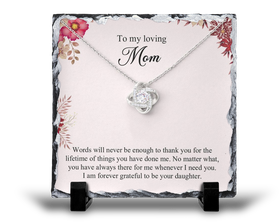
To My Loving Mom Birthday Christmas Mother's Day Gift Rock Slate | Shop

I'm A Survivor Breast Cancer Birthday Christmas Mother's Day Gift Mug

Mother S Day Gift Box With Flowers And Heart Decorations, Gift Box