The Heartbreaking Truth Behind May 2nd Birthdays: Leaked Documents Reveal All!
Have you ever wondered if your birthday could be more than just a celebration? What if the date you were born holds secrets that powerful institutions would rather keep hidden? Recent leaked documents have uncovered startling connections between May 2nd birthdays and a web of conspiracy, intrigue, and controversy that spans decades. From Jeffrey Epstein's notorious birthday book to classified military intelligence, these revelations paint a picture far more complex than anyone could have imagined.
The Urban Legends and Myths Surrounding May 2nd
The definitive internet reference source for urban legends, folklore, myths, rumors, and misinformation has long been a go-to resource for those seeking to separate fact from fiction. When it comes to May 2nd birthdays, however, the line between truth and legend becomes increasingly blurred. Online forums and conspiracy theory websites have been abuzz with speculation about the significance of this particular birth date, with some claiming it's linked to secret societies and others suggesting it's a marker for surveillance by intelligence agencies.
One persistent myth suggests that individuals born on May 2nd are more likely to be targeted for recruitment by clandestine organizations. While this claim lacks scientific backing, the recent document leaks have added fuel to the fire of speculation. As we delve deeper into the leaked materials, we'll explore whether there's any substance to these claims or if they're simply the product of overactive imaginations.
- The Truth About Epsteins Death Secret Files Leaked Show Hes Alive And Kicking
- Babylon Ny Secret Jeffrey Epsteins Md And The Nude Sex Parties
The Epstein Connection: A Birthday Book Revelation
In a shocking turn of events, a US congressional panel has released a redacted copy of an alleged birthday book given to Epstein. This document, part of the larger Epstein files, has sent shockwaves through political and social circles. The birthday book, which contains names, dates, and personal details of Epstein's extensive social network, lists numerous individuals with May 2nd birthdays.
The Epstein files are described as a partially released collection of millions of documents, images, videos, and emails detailing the activities of American financier and convicted child sex offender Jeffrey Epstein, including his social circle of public figures, politicians, and celebrities. Among these files, the birthday book stands out as a particularly intriguing piece of evidence, suggesting that Epstein may have used birthdays as a method of categorizing and potentially targeting individuals within his network.
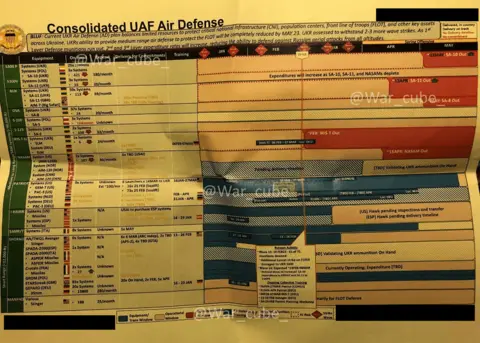
Ukraine's Spring Offensive and Classified Intelligence
Shifting gears from personal scandals to global geopolitics, Ukraine's spring offensive could yield modest gains, documents say. A cache of classified US documents leaked online sheds new light on American intelligence gathered about other countries. These documents, some marked as top secret, provide a detailed picture of the war in Ukraine and its potential outcomes.
- Leaked My Sisters Baby Photos Expose Secret Sex Scandal
- Leah Katebs Cancer Nightmare The Secret Doctors Are Hiding Will Shock You
Complete with timelines and dozens of impenetrable military acronyms, the documents paint a complex picture of the conflict. They reveal not only the strategic considerations of both sides but also the deep involvement of the United States in gathering intelligence on Russia. The leak has sparked debates about national security, the ethics of whistleblowing, and the delicate balance between transparency and operational security.
The Source of the Leak: Jack Teixeira's Arrest
The massive leak of US government secrets that has exposed spying on allies, revealed the grim prospects for Ukraine's war with Russia, and ignited diplomatic fires can be traced back to one individual. Jack Teixeira, 21, a member of the Massachusetts Air National Guard was arrested Thursday in connection to the investigation of leaked classified documents.
Teixeira's arrest has raised questions about security protocols within the military and the ease with which classified information can be accessed and disseminated. The documents he allegedly leaked include highly sensitive reports related to the war effort in Ukraine, including data on US intelligence capabilities and assessments of Russian military strength.
The Digital Age of Gossip and Information
In today's fast-paced digital world, information spreads at an unprecedented rate. Wesmirch distills the latest buzz from popular gossip blogs and news sites every five minutes, demonstrating how quickly news and rumors can circulate. All articles are selected via computer algorithm, vividly demonstrating that computers have a very long way to go before actually accomplishing truly intelligent work.
This rapid dissemination of information has both positive and negative implications. On one hand, it allows for quick access to news and the ability to fact-check in real-time. On the other hand, it can lead to the spread of misinformation and the amplification of conspiracy theories. The May 2nd birthday revelations are a prime example of how quickly speculation can turn into accepted "fact" in the digital age.
The Birthday Paradox and Personal Security
While the leaked documents have raised questions about the significance of May 2nd birthdays, it's important to consider the broader implications of sharing personal information like birth dates. In all cases, there is no security related system that depends only on your birthday to fulfill any step of authentication because may be your birthday is already mine according to the birthday paradox.
The birthday paradox states that in a group of just 23 people, there's a 50% chance that two people share the same birthday. This mathematical concept highlights the importance of not relying solely on easily obtainable information like birthdays for security purposes. As we navigate an increasingly digital world, it's crucial to be mindful of the information we share and how it can be used.
Protecting Your Personal Information
Given the revelations from the leaked documents and the potential risks associated with sharing personal information, it's more important than ever to be vigilant about your digital footprint. But of course, the less you reveal about yourself the safest you are. Here are some practical steps you can take to protect your personal information:
- Be cautious about sharing your full birth date on social media platforms.
- Use two-factor authentication whenever possible, opting for methods that don't rely solely on personal information.
- Regularly review your privacy settings on social media and other online accounts.
- Be wary of unsolicited requests for personal information, even if they appear to come from legitimate sources.
- Consider using a virtual private network (VPN) to add an extra layer of security when browsing online.
The Impact on Celebrities and Public Figures
The leaked documents have not only affected ordinary citizens but have also had significant implications for celebrities and public figures. Access delivers the best in entertainment and celebrity news with unparalleled video coverage of the hottest names in Hollywood, movies, TV, music and pop culture. The intersection of celebrity culture and leaked information has created a perfect storm of public interest and media scrutiny.
Many celebrities born on May 2nd have found themselves suddenly under the microscope, with their connections and associations being analyzed in light of the Epstein revelations. This has led to a broader discussion about privacy, the right to be forgotten, and the ethical responsibilities of both media outlets and consumers of celebrity news.
The WikiLeaks Connection
The world of leaked documents and classified information is not new, as evidenced by the long-standing work of organizations like WikiLeaks. Today, 5th August 2021, WikiLeaks publishes the Intolerance Network over 17,000 documents from internationally active right wing campaigning organisations HazteOir and CitizenGO. This release demonstrates the ongoing tension between government secrecy and the public's right to know.
While the WikiLeaks documents focus on a different subject matter than the May 2nd birthday revelations, they highlight the complex ethical landscape surrounding the publication of classified or sensitive information. The debate over what information should be made public and what should remain secret continues to evolve in the digital age.
Conclusion
The leaked documents surrounding May 2nd birthdays have opened a Pandora's box of questions about privacy, security, and the nature of information in the digital age. From the shocking revelations in Jeffrey Epstein's birthday book to the geopolitical implications of classified military intelligence, these leaks have far-reaching consequences that extend well beyond a single date on the calendar.
As we navigate this complex landscape, it's crucial to approach information with a critical eye, question sources, and be mindful of the personal data we share. The truth behind May 2nd birthdays may be more mundane than conspiracy theories suggest, but the broader implications of these leaks serve as a stark reminder of the power of information – and the importance of protecting it.
In an era where a 21-year-old National Guard member can allegedly access and leak top-secret documents, and where algorithms can spread gossip and rumors at lightning speed, we must all be more vigilant about our personal information and more discerning about the news we consume. The heartbreaking truth may not be in the significance of a particular birthday, but in our collective vulnerability to information warfare and the erosion of privacy in the digital age.
- Bill Gates Nude Photos Leaked In Epstein Scandal The Disturbing Truth Revealed
- The Nude Photos Epstein Was Hiding Shocking Truth About His Suicide

Leaked documents reveal U.S. eavesdropped on U.N. Secretary General

Ukraine war: Russian state media retract report of Russian retreat
Jack Teixeira's charges in full: 'Top secret' access, leak searches and