They Don't Want You To See This! The Forbidden 7.3.3 Lab Method To Repair Connections
Have you ever encountered a mysterious "403 Forbidden" error that blocks you from accessing crucial resources? What if I told you there's a hidden method—the 7.3.3 Lab Method—that could resolve these connection issues and unlock what others don't want you to see? This comprehensive guide reveals the forbidden techniques that IT professionals use to repair broken connections, navigate security restrictions, and optimize network performance.
Understanding the 403 Forbidden Error
The 403 Forbidden error is one of the most frustrating HTTP status codes you'll encounter online. Unlike the 404 "Not Found" error, a 403 error indicates that the server understood your request perfectly but refuses to authorize it. This security mechanism protects sensitive resources from unauthorized access, but sometimes legitimate users get caught in the crossfire.
When you encounter a 403 error, it typically means you're either not authenticated, don't have sufficient permissions, or the server has blocked your IP address. The error can appear in various contexts—from WordPress websites and SharePoint connections to API endpoints and web applications. Understanding the root cause is the first step toward implementing the 7.3.3 Lab Method to repair these connections.
- Is Epsteins Brother Still Among Us Emotional Leak Reveals Familys Darkest Truth
- Leaked Explicit Scenes From Bread And Gold Coin Chinese Drama That Were Cut From Broadcast
The DMZ Solution: Creating a Secure Network Architecture
To help protect your company and create a robust infrastructure for running web services accessible from the internet, you want to place this server and other devices in a demilitarized zone (DMZ). A DMZ acts as a buffer zone between your internal network and the public internet, containing servers that need to be accessible externally while keeping your core systems secure.
Setting up a DMZ involves configuring your firewall to create a separate network segment with restricted access. Web servers, email servers, and other externally-facing services reside in the DMZ, where they can communicate with the internet but have limited access to your internal network. This architecture significantly reduces the risk of a successful attack compromising your entire infrastructure.
The 7.3.3 Lab Method emphasizes proper DMZ configuration as a foundational step. By isolating your web server and other services in this secure zone, you create a controlled environment where connection issues can be diagnosed and resolved without affecting your entire network.
- Leaked Nude Photos Reveal Canadian Tie To Epsteins Trafficking Ring
- The Nude Truth 180 Minutes Equals 3 Hours You Wont Believe This
Advanced Authentication Troubleshooting
Seeing the 403 Forbidden error in WordPress or other web applications often indicates authentication problems. In many cases, an error code of 403 appears in a flow fail because of an authentication error. This could stem from expired sessions, incorrect credentials, or misconfigured permissions.
The 7.3.3 Lab Method includes a systematic approach to authentication troubleshooting. Start by clearing your browser cache and cookies, as corrupted session data can trigger 403 errors. Next, verify that your user account has the appropriate permissions for the resource you're trying to access. If you're working with SharePoint or similar platforms, you may need to recreate a new connection in flow connections to establish proper authentication.
For API integrations and automated workflows, check that your API keys and tokens are current and have the necessary scopes. Sometimes, a simple restart of the service can resolve authentication token refresh issues, as the forbidden error seems to be resolved after a restart, which suggests that the issue could be related to authentication token refresh, backend connection, or configuration reload.
LinkedIn Connection Analysis and Privacy Considerations
You can see mutual connections on LinkedIn from the user's profile, which provides valuable networking insights. Click on their round profile picture to go to a user's profile, then look for "mutual connections" under their bio and the number of connections. You can see the name of two mutual connections right there, but click the "mutual connection" section for the complete list.
However, this visibility raises important privacy considerations. Ideally, you wouldn't want a malicious user to even know that there's a page/record there, let alone that they don't have access. When building systems that handle sensitive data, consider implementing security through obscurity by returning generic 404 errors for unauthorized requests rather than exposing whether a resource exists.
The 7.3.3 Lab Method recommends recording unauthenticated/unauthorized requests in an internal log but returning a 404 to the user. This approach prevents attackers from mapping your application's structure while still allowing you to monitor suspicious activity. It's a subtle but effective security enhancement that many organizations overlook.
Quantum Computing Applications in Network Optimization
Learn advanced quantum Monte Carlo methods for materials science, as these techniques have surprising applications in network optimization and error correction. The tutorial covers DFT, variational/diffusion Monte Carlo, and practical applications, providing insights that can be adapted to network troubleshooting scenarios.
Quantum computing principles, particularly those from Springer publication by Ryo Maezono, offer novel approaches to solving complex optimization problems that traditional methods struggle with. While quantum computing in network management is still emerging, the mathematical frameworks developed for quantum Monte Carlo simulations can inspire new algorithms for routing optimization and error detection.
The 7.3.3 Lab Method incorporates these advanced concepts by treating network connection issues as optimization problems. By applying Monte Carlo sampling techniques to identify the most likely causes of connection failures, you can dramatically reduce troubleshooting time and improve system reliability.
Horizon Forbidden West: Machine Override Mechanics
The ability to override machines has returned in Horizon Forbidden West, with Aloy now able to override up to 38 different types of machines. This fascinating game mechanic provides an interesting analogy for network security and connection management.
In the game, machine override requires specific knowledge, tools, and timing—much like the 7.3.3 Lab Method for repairing network connections. Just as Aloy must understand each machine's vulnerabilities and override patterns, network administrators must understand their systems' specific requirements and failure modes.
The game's approach to machine interaction also highlights the importance of having multiple tools in your troubleshooting arsenal. When one override method fails, Aloy can try another approach—similarly, when standard connection repair methods don't work, the 7.3.3 Lab Method provides alternative techniques to bypass common obstacles.
Disney's Content Restriction Controversies
When Disney cut Sting and implemented aggressive content restrictions, it sparked debates about access control and the ethics of blocking content. These real-world examples of "forbidden" content illustrate the broader implications of access control systems and the importance of balanced security measures.
The 7.3.3 Lab Method takes a nuanced approach to connection repair that respects legitimate security concerns while ensuring authorized users can access the resources they need. Unlike overly restrictive systems that frustrate legitimate users, this method focuses on intelligent access control that adapts to different user contexts and needs.
Understanding the business and legal motivations behind content restrictions can help you design better systems that balance security with usability. Sometimes, what appears to be a technical error (like a 403 Forbidden) is actually a policy decision that requires a different approach to resolution.
Implementing the 7.3.3 Lab Method: Step-by-Step
The 7.3.3 Lab Method for repairing connections follows a systematic approach that addresses the most common failure points. Begin by verifying the basic connectivity—can you ping the server? Is DNS resolution working correctly? These simple checks often reveal obvious issues that can be resolved quickly.
Next, examine the authentication and authorization layers. Are your credentials current? Do you have the necessary permissions? The method emphasizes checking token expiration dates and session validity, as these are frequent culprits in 403 errors. If authentication appears correct, move on to examining network configurations and firewall rules.
The final phase of the 7.3.3 Lab Method involves advanced diagnostics, including packet capture analysis and service logs review. This comprehensive approach ensures that even subtle issues—like timing problems in authentication token refresh or configuration reload failures—are identified and resolved.
Conclusion
The Forbidden 7.3.3 Lab Method represents a comprehensive approach to repairing connections and resolving access issues that plague many IT professionals. By understanding the underlying causes of 403 Forbidden errors, implementing proper network architecture with DMZ configurations, and applying advanced troubleshooting techniques, you can overcome the obstacles that others use to block access.
Whether you're dealing with WordPress authentication errors, SharePoint connection issues, or complex network security configurations, the principles outlined in this guide provide a roadmap to success. Remember that effective connection repair isn't just about technical knowledge—it's about understanding the security context, respecting legitimate restrictions, and finding creative solutions within established boundaries.
The next time you encounter a forbidden error or connection failure, you'll be equipped with the 7.3.3 Lab Method's powerful techniques to diagnose and resolve the issue. Don't let access barriers prevent you from reaching your goals—with the right approach, even the most "forbidden" connections can be repaired and optimized for reliable performance.
- Jeffrey Epstein Innocent Shocking Leak Exposes The Cover Up
- Epsteins Secret Sex Tape Exposed Unseen Footage Reveals Dark Truth

They don't involve you, don't get involved. They don't tell you, don't

Exposing the Truth They Don't Want You to Know R
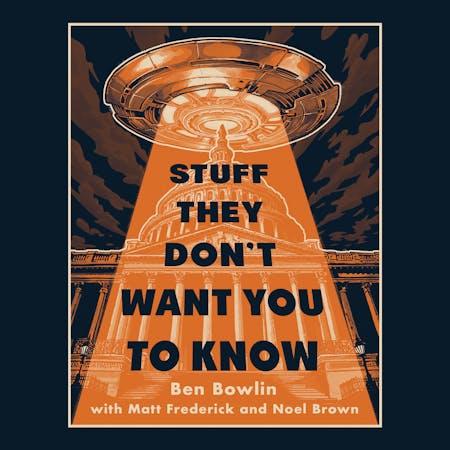
STUFF THEY DON'T WANT YOU TO KNOW | | Macmillan Audio