This Shocking IPhone Hack Turns 20 Questions Into A Porn Leak – Try It Now!
Have you ever wondered how a simple guessing game could lead to the most devastating privacy breach of your life? What if I told you that a seemingly innocent iPhone feature could be exploited to turn your private photos into a public spectacle? The shocking truth is that many iPhone users are completely unaware of how vulnerable their devices really are.
In today's digital age, where smartphones contain our most intimate moments, understanding the risks and knowing how to protect yourself isn't just smart—it's essential. This article will reveal the shocking reality of iPhone privacy vulnerabilities and provide you with actionable steps to secure your digital life before it's too late.
Understanding What Makes Something "Shocking"
The meaning of shocking is extremely startling, distressing, or offensive. When we encounter something shocking, it typically causes intense surprise, disgust, horror, or moral outrage. In the context of technology and privacy breaches, shocking often refers to events that violate our expectations of security and personal boundaries.
- Kat Timpfs Due Date Leaked The Scandalous Truth Will Blow Your Mind
- Madison Scotts Nude Leak The Humiliating Public Disgrace That Broke The Internet
How to use shocking in a sentence? Consider this: "The revelation that millions of private photos were accessed through a simple security flaw was genuinely shocking to users worldwide." This demonstrates how the term applies to unexpected violations of privacy that leave people feeling vulnerable and betrayed.
Causing intense surprise, disgust, horror, or offense, shocking events often occur when technology fails us in ways we never anticipated. The emotional impact of discovering that your private moments have been exposed to strangers can be truly devastating, leading to feelings of violation and helplessness.
The Anatomy of a Privacy Disaster
You can say that something is shocking if you think that it is morally wrong. It is shocking that nothing was said when millions of users' private photos were accessed through security vulnerabilities. This was a shocking invasion of privacy that exposed countless individuals to public scrutiny and potential exploitation.
- Epsteins Secret Leak Daily Mail Publishes Nude Photos And Trafficking Ring Details
- Cute Dream Date Exposed How He Knew Every Detail The Shocking Leak You Must See
Shocking synonyms include appalling, outrageous, scandalous, and disgraceful. The pronunciation of "shocking" is /ˈʃɒkɪŋ/, and understanding its translation across different languages helps us recognize how universally disturbing privacy violations are perceived. The English dictionary definition of shocking encompasses anything that causes moral or emotional distress.
According to the Oxford Advanced Learner's Dictionary, shocking as an adjective describes something extremely bad or unpleasant, or of very low quality. When applied to technology, it often refers to security failures that compromise user trust and personal safety.
The Reality of Digital Privacy Breaches
Shocking refers to something that causes intense surprise, disgust, horror, or offense, often due to it being unexpected or unconventional. It could relate to an event, action, behavior, news, or revelation that departs drastically from normal standards or expectations. In the digital world, shocking often involves the unexpected exposure of private information.
The adjective shocking (comparative more shocking, superlative most shocking) inspiring shock has become increasingly relevant as technology advances. What was once considered impossible or highly unlikely is now a daily reality for many users who discover their private data has been compromised.
Recent news and headlines from major tech publications have revealed numerous shocking privacy breaches. The images were obtained via the online storage offered by Apple's iCloud platform for automatically backing up photos from iOS devices, such as iPhones. This method of attack, often referred to as "the 20 questions hack," exploits security questions to gain unauthorized access.
How the "20 Questions" Hack Works
The "20 questions" method is a social engineering technique where attackers gather personal information through seemingly innocent conversations or by exploiting publicly available data. Once they have enough information, they can answer security questions and reset passwords, gaining access to accounts without the user's knowledge.
This shocking vulnerability exists because many people use easily guessable information for their security questions. Birthdates, pet names, childhood addresses, and mother's maiden names are often available through social media or public records. When combined with the ability to reset passwords through these questions, it creates a perfect storm for privacy invasion.
The hack typically follows a pattern: attackers identify potential targets, research their backgrounds, and systematically work through security questions until they gain access. Once inside, they can download entire photo libraries, access messages, and even track the victim's location through Find My iPhone features.
Real-World Consequences of Privacy Breaches
The most shocking aspect of these privacy violations isn't just the technical breach—it's the human impact. Victims often experience severe emotional distress, anxiety, and depression following the exposure of their private photos. The feeling of being watched, judged, and violated can be overwhelming.
Many victims report feeling powerless and embarrassed, leading some to withdraw from social activities or change their appearance to avoid recognition. The psychological trauma can last for years, affecting relationships, careers, and overall quality of life. Some victims even experience physical symptoms like insomnia, panic attacks, and digestive issues due to the stress.
The financial consequences can be equally devastating. Some victims face extortion attempts, where attackers threaten to release more photos unless paid. Others may lose job opportunities or face discrimination when employers discover the leaked content. The cost of legal action to remove content from websites can also be substantial.
Protecting Yourself from Shocking Privacy Breaches
Understanding that shocking weather can be predicted and prepared for, we must apply the same principle to digital privacy. Shockingly, many users continue to use weak passwords and obvious security question answers, leaving themselves vulnerable to the very attacks we've discussed.
To protect yourself, start by enabling two-factor authentication on all accounts. This adds an extra layer of security beyond just a password. Use a password manager to create and store complex, unique passwords for each service. When setting up security questions, treat them like additional passwords—use random answers that cannot be guessed or researched.
Regularly review your privacy settings on all platforms, and be cautious about what personal information you share online. Consider using a separate email address for sensitive accounts, and never use the same password across multiple services. These simple steps can dramatically reduce your risk of becoming a victim.
The Role of Tech Companies in Privacy Protection
Lifehacker has been the world's leading guide to tech and life tips, tricks and hacks since 2005. Our job is to figure out how tech, gadgets, software, and other things work so you don't have to. However, even the most tech-savvy users can fall victim to sophisticated privacy attacks.
Tech companies have a responsibility to protect user data, but they cannot do it alone. Users must also take an active role in their own security. This includes staying informed about potential threats, regularly updating software, and being cautious about granting app permissions.
The shocking reality is that even major companies with vast resources can be vulnerable to attacks. The iCloud breach that affected numerous celebrities demonstrated that no system is completely secure. This underscores the importance of personal responsibility in digital security.
Celebrity Privacy Breaches: A Wake-Up Call
Radar has collected a list of the most notable naked celebrity hacks of all time. From Megan Kelly to Kim Kardashian, hacked devices have led to these stars' most intimate photos being leaked for public consumption. These high-profile cases serve as shocking reminders of how vulnerable we all are.
The celebrity hacks often involve the same "20 questions" technique we discussed earlier. Attackers research public information about celebrities, then use that knowledge to answer security questions and gain access to their accounts. The resulting leaks can affect not just the celebrities but also their friends, family members, and associates.
These incidents have sparked important conversations about digital privacy, consent, and the ethics of sharing private content. They've also highlighted the need for better security practices and more robust legal protections for victims of privacy violations.
The Legal Landscape of Digital Privacy
The shocking truth about privacy laws is that they often lag behind technological advancements. While some jurisdictions have enacted strong privacy protections, many areas still lack adequate legal frameworks to address digital privacy violations effectively.
In the United States, for example, there is no comprehensive federal law protecting digital privacy. Instead, a patchwork of state laws and industry-specific regulations creates a confusing landscape for both users and companies. This legal uncertainty can make it difficult for victims to seek justice or compensation.
Some countries have taken stronger stances on digital privacy. The European Union's General Data Protection Regulation (GDPR) provides comprehensive protections for personal data and imposes significant penalties for violations. However, enforcement remains a challenge, and determined attackers often operate from jurisdictions with weak or non-existent privacy laws.
Moving Forward: Building a Culture of Digital Privacy
Creating a culture that values digital privacy requires effort from individuals, companies, and governments alike. We must recognize that our digital lives are just as important as our physical ones and deserve the same level of protection and respect.
Education plays a crucial role in this cultural shift. Schools should teach digital literacy and privacy awareness as fundamental skills. Companies should prioritize user privacy in their product design and be transparent about their data practices. Governments should enact and enforce strong privacy laws that keep pace with technological developments.
The shocking reality of privacy breaches should serve as a catalyst for positive change. By understanding the risks and taking proactive steps to protect ourselves, we can create a digital environment where privacy is respected and personal information is secure.
Conclusion
The shocking truth about iPhone privacy vulnerabilities, particularly the "20 questions" hack, reveals a fundamental weakness in how we approach digital security. What starts as a simple guessing game can quickly escalate into a devastating privacy breach that affects every aspect of a victim's life.
However, knowledge is power. By understanding how these attacks work, recognizing the warning signs, and implementing strong security practices, you can significantly reduce your risk of becoming a victim. Remember that digital privacy is not just about technology—it's about protecting your dignity, your relationships, and your peace of mind.
The next time you hear about a shocking privacy breach, don't just think about the technical details. Consider the human impact and ask yourself: "What would I do if this happened to me?" Then take the necessary steps to ensure that you never have to find out the hard way. Your digital life is worth protecting, and the time to start is now.
- Exclusive Leak The Forbidden Technique To Perfect Fishtail Braids In Seconds
- Leaked The Secret Symbolism Of Tamlin Tattoos That Everyone Is Obsessed With

This DIY hack turns old phones into watchdogs

Rough "hack" turns calculator into ultimate cheating tool - by
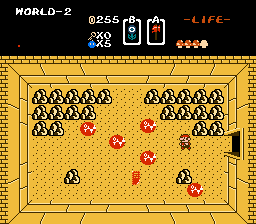
ROM Hack Turns Zelda 1 Into a Mario Game - Gaming Reinvented